
Suppose you are trying to log in to your bank using your password in a mobile banking application, the bank may ask you to verify the OTP sent to your registered mobile number before giving you access.
This is an example of zero trust security using Multi-Factor Authentication (MFA).
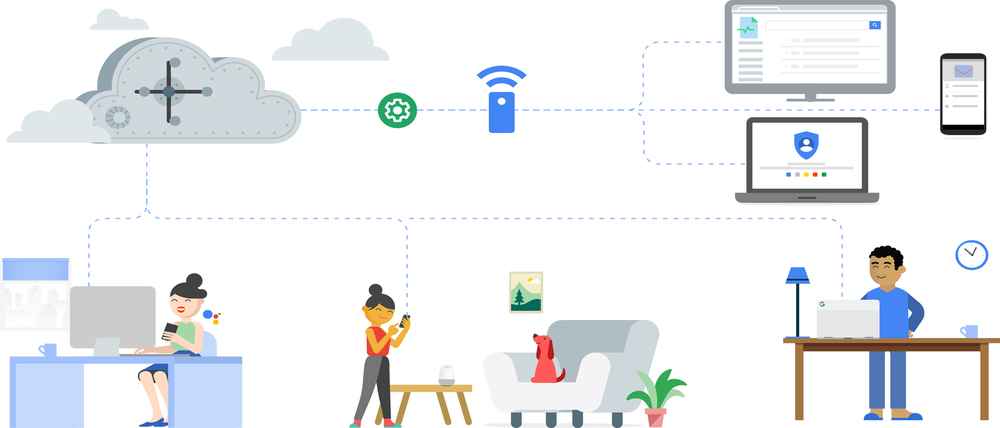
Zero trust is a security model in which trust is set to a neutral state.
Trust is not given to an individual or institution but instead is based on the decisions of large groups of individuals and institutions. Zero trust security can be found in financial institutions, hospitals, and government agencies.
Zero trust security is a security model that is based on the principle that “trust only goes as far as you can verify”.
This model is applied to organizations that wish to implement security without the traditional reliance on a trusted third party to provide access control. Instead, each party’s trustworthiness is verified by the other party. In this model, the assumption is that no party is trusted.
Why zero trust?

For example, if a website is not using zero trust security, a hacker can easily exploit a vulnerability in the website and gain access to it.
Zero trust security helps to eliminate this vulnerability and protect the website from hackers.
It is a philosophy that says we should not trust anything on the Internet and that instead, we should focus on the here and now. Zero trust security is the idea that instead of trying to protect users from outside attackers, we should focus on protecting the user from themselves.
There are three principles of zero trust security that are important to understand.
They are:
1. Explicit verification
2. Use least privileged access
3. Assume breach
1. Explicit verification
Always authenticate and authorize based on all available data points, such as user identification, location, device health, service or workload, or data classification.
2. Use least privileged access
The zero trust model implements least-privilege access by restricting user access to only the resources that are necessary for a given role. It also supports the identification, monitoring, and control of networked devices.
3. Assume breach
Instead of assuming everything behind the corporate firewall is safe, the zero trust model assumes breach and verifies each request as though it originates from an open network.
Zero trust security is a philosophy that focuses on minimizing risk and maximizing security.
What are the benefits of zero trust?
The benefits of implementing zero trust security include a reduction of risk, easier adoption of security updates, and a reduction of the number of false negatives.
Zero trust security is still new, but it is becoming more widely implemented by companies such as Apple, Microsoft, and Google.
Regardless of your organization, always respond this way;
“I have zero trust in you! I need to verify you first before I can trust you and grant access to the resource you want.”
Adhere to the philosophy “never trust, always verify” for every access request.









